Methods to save IT
Mobile Hotspot is a portable device and a portable gaming device. It functions the same way like a USB modem, relying on a service provider’s mobile broadband, and providing connectivity within a range of about 30 feet.
Benefits of Mobile Hotspots:-
It is good for frequent travelers, needing fast connectivity. It provides an anytime, anywhere high-speed connectivity, and it is like having a dedicated connection. One can freely work independent of the risks of unsecured public Wi-Fi connection.
One can save on the battery life and phone data plan, work longer without connection drop, choose the best smartphone cellular carrier on own terms.
Disadvantages of Mobile Hotspots:
While translating connections from 4G to Wi-Fi some mobile hotspot devices need continuous charging. Also, an excessive energy requirement or a depletion in connection speed may result and faster battery draining out is big concern. Some devices may not receive calls due to no simultaneous support for voice and data.
Methods of Hacking
# Sending Spyware via Email:-
Hackers access the data by sending spyware from a known contact’s email. Be careful of dubious email having attachments.
# The Mysterious USB Drive:
Pen-drives at cyber cafes may deliberately be left by hackers. Do not view the files on it and be safe from the malware.
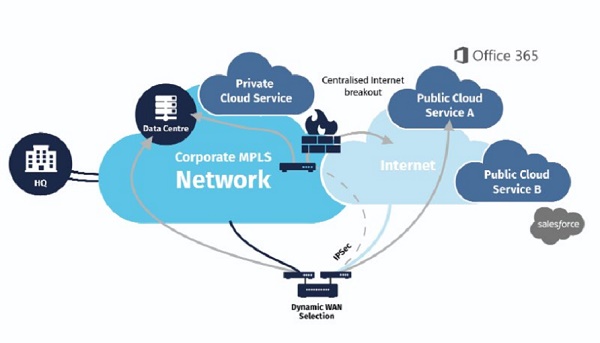
# Hotspots:
A public Wi-Fi hotspot though convenient, is a potential opportunity for hackers to gain access to user data and must be used very judiciously.
# Open Home Networks:
must be password protected to deny hackers the pleasure of causing nightmares to the user.
# High Resolution Cameras:
Be careful of unseen cameras that may record all login information. One should take care to avoid someone opportunity to see one feeding the sensitive data.

# Phone to Phone:
While talking on phone or browsing one should be careful of any persons in the proximity and avoid to them an open gateway to the device.
# The Not-Missing Device:
Be careful of a phone forgotten somewhere, left unattended for long or returned. One needs to be very careful while using the device.
# Malicious Websites:
A casual access of very attractive websites luring with excellent offers, may result in malware installation in one’s device.
# Public Access Networks:
The open networks created to communicate quickly with other devices, may offer opportunity to hackers to gain access to the user data.
# Buying Used Devices:
Run a professional scan, before using second-hand devices.
Protection Against Hacking
While our digital devices are highly vulnerable to hacking, there are ways one may follow and be safe enough.
Some of them may include:
# Know the Surroundings:
Avoid access to private and sensitive information in public places, like bank accounts etc. Mobile searches should be minimum as per urgent needs only, one must be aware of any suspicious characters around.
Updated Antivirus Program:
We need protections against viruses, and malicious programs. A regular update ensures adequate safety.
# Virtual Private Network (VPN):
A VPN hides the IP address, encrypts all incoming and outgoing traffic, making it difficult for hackers to steal sensitive private information.






























